
Delivering security solutions that meet business objectives…
and keep you safe.
Status quo is not an option in today’s competitive economic climate. Organizations need solutions that help them exceed expectations at the right price. In an economic downturn, it is more important than ever to leverage information technology to deliver business solutions that help your business stay competitive. Maintaining and enhancing legacy applications and infrastructure while taking advantage of new technology and systems becomes a very challenging task. Adding on pressures from audits, data protection, providing access to the right data at the right time, and disaster recovery creates a tenuous situation that needs constant balancing and rightsizing.
DG Technology is uniquely qualified to supply security management across all systems.
We partner with the best information security providers to secure your infrastructure from attacks and ensure you meet compliance requirements including:
Mapping compliance requirements, business objectives and market trends to specific technology solutions can be overwhelming. DG Technology helps companies navigate the process — from assessment and architecture development to deployment and support.
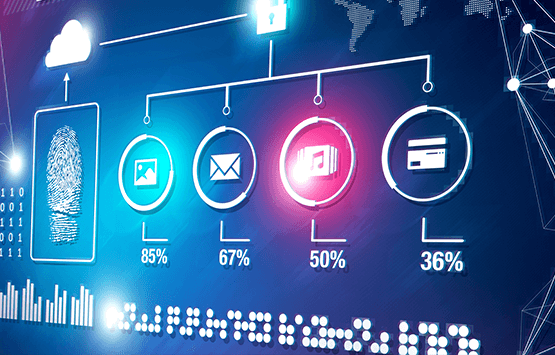

Focusing on delivering a comprehensive security strategy, solutions and protection across all platforms – desktop to mainframe.
While cost containment may be the top business priority today, IT has to fulfill its primary purpose – enabling business. Security and compliance play a crucial role in this. DG Technology can help you ensure business continuity, while protecting critical data, enhancing web services, proving compliance, and save time and money in the process.
© 2025 DG TECHNOLOGY CONSULTING LLC
